Computer viruses remain one of the most persistent digital threats in 2025, with file infector variants accounting for 37% of all malware attacks worldwide. Despite advances in cybersecurity, these malicious programs continue to evolve, finding new ways to compromise system files and evade detection. Particularly concerning is how modern viruses can remain dormant for months before activating, giving them ample time to spread across networks and cause significant damage.
The infector virus has become increasingly sophisticated, targeting not just traditional executable files but also cloud-based applications and containerized environments. These malicious programs attach themselves to critical system components, consequently corrupting data, stealing sensitive information, or creating backdoors for additional malware. Furthermore, today’s file infectors often employ advanced polymorphic code that changes its signature with each infection, making traditional detection methods largely ineffective.
This article explores how these digital threats operate in 2025’s computing landscape, examining their infection patterns, distribution mechanisms, and stealth techniques. We’ll also provide practical strategies to protect your systems against these evolving threats, including the latest AI-powered detection tools and security practices essential for maintaining digital safety in an increasingly vulnerable environment.
What Makes File Infector Viruses Dangerous in 2025
File infector viruses have become increasingly sophisticated in 2025, presenting unique dangers that make them especially challenging to detect and remove. Unlike other malware types, these viruses directly integrate with legitimate system files, creating persistent threats that can compromise entire networks.
Executable File Targeting: .exe, .dll, and .com
The primary danger of file infector viruses stems from their ability to attach to executable files that users frequently access. These viruses specifically target critical program files with extensions like .exe, .dll, and .com, which form the backbone of any operating system 1. When an infected file is launched, the virus activates and begins installing itself throughout the system 1.
What makes this approach particularly effective is how these viruses weaponize trusted applications. Rather than arriving as obvious malware, they hide within legitimate programs that users run regularly. This parasitic behavior enables them to:
- ): Spread rapidly across systems by scanning for other executable files to infect
- ): Maintain persistence through frequent execution of common programs
- ): Cause widespread compatibility issues by corrupting shared DLL files
- ): Generate sluggish performance and unexpected program crashes
The most concerning aspect is that many organizations still run outdated software vulnerable to such attacks. Moreover, when these viruses target shared libraries (.dll files), a single infection can compromise multiple applications simultaneously.
Memory-Resident Behavior in Modern OS
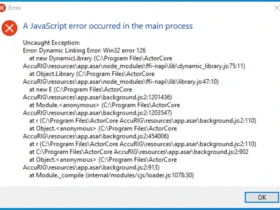
Memory-resident viruses represent one of the most dangerous variants of file infectors in 2025’s computing landscape. Unlike traditional viruses, these threats load their replication module directly into RAM, allowing them to operate independently even after the host application terminates.
Once established in memory, these viruses actively interfere with programs while they’re running. They consume system resources, modify memory allocation, and intercept system calls that applications make to the operating system. Additionally, they can attach themselves to anti-virus applications, allowing them to infect any file scanned by security programs.
This persistent memory presence creates significant removal challenges. Traditional scanning often fails because the virus isn’t stored in a single file location. In many cases, the virus blocks antivirus actions directly from memory, requiring specialized removal tools or complete system reformatting.
Polymorphic and Metamorphic Code Variants
Perhaps the most sophisticated aspect of modern file infector viruses is their ability to continuously change their appearance through polymorphic and metamorphic techniques. These variants employ advanced obfuscation to evade detection by traditional security tools.
Polymorphic viruses use encryption keys to change their shape and signature while maintaining their malicious functionality. They consist of two parts: an encrypted virus body that changes its shape, and a decryption routine that remains constant. Through techniques like dead-code insertion, register reassignment, and instruction substitution, these viruses can rapidly evolve into new versions that signature-based detection cannot identify.
Even more concerning are metamorphic viruses, which completely rewrite their code with each iteration without using encryption keys. Unlike polymorphic variants, no part of a metamorphic virus remains constant, nor does it ever return to its original form. This complete transformation makes them extraordinarily difficult to detect using traditional methods.
The distinction matters significantly for security responses. While polymorphic malware requires entry point algorithms for detection, metamorphic variants demand geometric detection or tracing emulators. This technical distinction highlights why traditional signature-based security approaches increasingly fail against modern file infector threats.
Types of File Infector Viruses and Their Infection Patterns
Modern file infector viruses come in several distinct forms, each with unique infection patterns and attack vectors. Understanding these variants helps identify potential threats before they compromise critical system components.
Macro Viruses in Office Files
Macro viruses target text-based documents generated by office applications like Microsoft Word, Excel, and PowerPoint. Instead of attacking executable files, they use the macro programming languages built into these applications to execute malicious code. When an infected file is opened, the embedded macro virus activates automatically if macros are enabled.
These viruses spread primarily through email attachments and shared files. Once activated, they can corrupt documents, manipulate data, and even access address books to send infected files to contacts. The infamous Melissa virus exemplifies this approach—after infecting a Word document, it emailed itself to the first 50 contacts in the victim’s address book, causing approximately $80 million in damage.
What makes macro viruses particularly troublesome is their cross-platform nature; they can affect both Windows and Mac systems using identical code. Microsoft addressed this threat by disabling macros by default in Office versions since 2000, forcing attackers to trick users into enabling these features.
System Infector Viruses in Boot Sectors
System infector viruses attack the boot sector—a reserved area containing code needed to start the operating system. These viruses specifically target the Master Boot Record (MBR) of hard disks or the boot sectors of storage devices.
When a computer boots from an infected disk, the virus loads into memory before the operating system starts. Once resident in memory, it traps BIOS functions (typically disk interrupt vector Int 13h) to remain active, subsequently monitoring disk access to infect other media.
System infector viruses fall into two categories:
- ): Overwriting viruses: Replace the original boot sector with malicious code while preserving partition tables
- ): Relocating viruses: Save the original boot sector elsewhere on the drive, sometimes destroying areas and rendering disks unreadable
Although less common in 2025 due to BIOS architecture improvements that prevent modifications to the first sector of hard drives, these viruses remain dangerous since they execute before security software can load.
Sparse Infectors and Low-Frequency Attacks
Sparse infector viruses employ a strategic approach—they infect files only under specific conditions to reduce detection probability. Unlike aggressive malware that rapidly infects multiple files, sparse infectors operate with restraint.
These viruses might activate only during the 10th execution of a program, target files within certain size ranges (like 128KB maximum), or remain dormant for extended periods before becoming active. This sporadic behavior creates a pattern where users experience symptoms briefly, then nothing for a while.
The deliberate infrequency of attacks makes sparse infectors extraordinarily difficult to detect through conventional scanning methods, as their activity patterns don’t trigger typical security alerts.
Multipartite Viruses with Dual Infection Vectors
Multipartite viruses represent the most sophisticated category, combining multiple infection techniques. Their genome is segmented into two or more parts, with each encapsulated in separate particles that appear to propagate independently.
These viruses simultaneously attack various system components—typically both files and boot sectors. This dual-vector approach creates persistent infections that traditional removal methods often fail to completely eliminate.
A defining characteristic of multipartite viruses is their need for concurrent presence of multiple segments to complete the replication cycle. This seemingly evolutionary drawback is balanced by increased adaptability, enabling multipartite viruses to colonize environments that monopartite forms cannot penetrate.
Remarkably, multipartite viruses can rise to dominance even without explicit microscopic advantages, primarily through ecological dynamics when interacting with host population structures. Their complex replication methods make them among the most challenging viruses to detect and remove.
How File Infector Viruses Spread Across Systems
File infector viruses employ sophisticated propagation techniques to move between systems, often remaining undetected until significant damage has occurred. Understanding these transmission vectors is essential for implementing effective protection strategies.
Attachment to Executable Files via Binary Injection
File infector viruses primarily spread by attaching themselves to executable files through a process called binary injection. When these viruses locate program files like .exe, .dll, or .com extensions, they modify the binary code, essentially “hitchhiking” alongside legitimate applications. The virus can insert itself at the beginning (prepending), end (appending), or within the code (call hooking).
Given that many viruses propagate by changing the file’s entry point, they execute first when an infected program launches. Afterward, they return control to the original application, making the infection nearly invisible to users. In essence, the virus executes its malicious payload prior to running the legitimate code, allowing it to search for other executable files to infect.
Replication Through Network Shares and USB Devices
Network shares and removable media remain among the most common transmission vectors for file infector viruses. According to Honeywell’s 2022 report, threats capable of spreading via USB devices increased from 37% in 2020 to 57% in 2021.
First and foremost, USB-based attacks occur when:
- ): An infected USB drive connects to a clean system, automatically executing malware
- ): Clean USB drives connect to infected systems, becoming carriers themselves
- ): Self-replicating code copies itself to new drives plugged into infected systems
Notably, these viruses can propagate through unmapped network drives and actively scan for other computers on local networks. This behavior enables rapid infection across organizational infrastructure, as shown by the threefold increase in USB-based attacks observed in early 2023.
Cloud Sync and Remote File Sharing Risks
In contrast to traditional belief, cloud storage can indeed become a vector for virus propagation. Although major services like OneDrive scan for malware, they aren’t infallible. Cloud storage risks include misconfiguration, insecure interfaces, and encryption issues that malware authors exploit.
File infectors can potentially spread when infected files sync across multiple devices through cloud storage platforms. In this case, if a virus infects a file that subsequently uploads to cloud storage, it may download to other connected devices before detection occurs.
Analogous to local file sharing, cloud syncing creates opportunities for malware to move laterally between systems. Even with built-in protection, cloud environments remain vulnerable to sophisticated attacks targeting file-sharing mechanisms, making them viable channels for modern file infector viruses to traverse organizational boundaries.
Stealth and Evasion Techniques Used by Modern File Infectors
In the arms race between security experts and malicious actors, file infector viruses have developed advanced stealth mechanisms to evade detection. These techniques allow computer viruses to remain hidden for extended periods, effectively bypassing modern security solutions.
Code Obfuscation and Encryption
Modern file infector viruses frequently employ code obfuscation to hide their true intent while maintaining functionality. This transformation makes malware significantly harder to detect, analyze, and reverse engineer. Typically, these viruses use encryption to conceal their malicious code, with a decryption loop that only reveals the actual virus when executed.
The most sophisticated examples include:
- ): Polymorphic viruses that rewrite their code on each infection while maintaining functionality. These generate unique decryptors for each instance while keeping the encrypted payload consistent.
- ): Metamorphic viruses that completely rewrite their code with each iteration without using encryption keys. Unlike polymorphic variants, no part remains constant, nor does it return to its original form.
Maintaining File Size to Avoid Detection
File size manipulation represents another method infector viruses use to bypass security tools. Binary padding adds junk data to change the on-disk representation of malware without affecting functionality. This technique works because many security scanners have hardcoded size limits—public file scanning services like VirusTotal restrict the maximum size of uploaded files.
Likewise, some malicious programs maintain their original file size after infection. The new generation of file infector viruses uses stealth mechanisms that encrypt their code while keeping infected structures the same size. This approach helps evade detection tools that flag size changes as potential infections.
Memory-Only Execution Without Disk Footprint
Perhaps the most effective evasion technique involves memory-only execution. These “fileless” attacks operate entirely in RAM without writing files to disk. Instead of using traditional malware that requires executable files, these threats exploit legitimate system tools and processes.
By 2023, fileless malware represented three-fourths of all malware incidents, growing at 72% over five years. Process hollowing exemplifies this approach—an attacker starts a legitimate process like notepad.exe but then replaces its original code with malicious code while keeping the process name intact.
Nevertheless, memory-only malware has one significant weakness—RAM is cleared when a system restarts. Hence, these viruses must establish persistence mechanisms or risk being removed during reboots.
Prevention and Protection Strategies for 2025
Protecting systems against file infector viruses requires a multi-layered defense approach. Nowadays, organizations must implement comprehensive strategies that address both technological and human vulnerabilities.
Heuristic and AI-Based Antivirus Detection
Modern protection relies heavily on advanced detection methods rather than simple signature matching. Heuristic analysis examines code for suspicious properties and behaviors that might indicate malicious intent. This approach works through both static methods—decompiling and examining source code—and dynamic techniques that run suspicious files in sandboxed environments to observe behavior. Currently, AI-backed solutions apply deep learning and neural networks to identify patterns and detect zero-day malware. These systems become increasingly accurate as they process more data, enabling them to recognize even previously unseen threats.
Application Whitelisting and Execution Control
Application whitelisting fundamentally changes how systems operate by allowing only approved applications to run while blocking everything else by default. This approach is particularly effective for industrial control systems with static components. Most importantly, whitelisting complements antivirus solutions by limiting executable programs to pre-approved ones, thereby preventing malware execution even when security tools fail to detect new threats. Organizations should implement whitelisting using file hashes or software signatures rather than weaker methods like file names.
Regular Backups and Patch Management
Maintaining regular, offline backups remains essential as no cybersecurity product is 100% effective all the time. Patch management involves systematically identifying, testing, and deploying software updates to fix known vulnerabilities. Therefore, organizations should prioritize patches addressing high-risk security issues that ransomware could exploit. Testing patches in controlled environments before deployment helps prevent compatibility problems.
User Awareness and Email Attachment Scanning
Email attachments continue serving as primary infection vectors. Organizations should focus on educating users through these key practices:
- ): Verify sender identities before opening attachments
- ): Save and manually scan attachments before opening
- ): Disable automatic attachment downloads in email clients
- ): Exercise caution with unexpected attachments, even from known contacts
- ): Create restricted-privilege user accounts for reading emails
Ultimately, effective protection involves both technological safeguards and informed users who recognize potential threats.
Conclusion
File infector viruses have undoubtedly become more sophisticated and dangerous since their early iterations. Their ability to hide within legitimate files while maintaining functionality makes them particularly insidious threats in our current digital ecosystem. Throughout this examination, we’ve seen how these malicious programs target various system components—from executable files to office documents and boot sectors—creating persistent infection vectors that traditional security measures struggle to combat.
The emergence of polymorphic and metamorphic variants further complicates detection efforts. These advanced threats continuously rewrite their code, effectively rendering signature-based security approaches obsolete. Additionally, techniques such as binary injection, memory-resident behavior, and fileless execution provide viruses with powerful evasion capabilities that bypass conventional security measures.
Transmission vectors likewise continue to evolve. USB devices remain significant threats despite increased awareness, while network shares and cloud storage services offer new opportunities for lateral movement between systems. This expanded attack surface demands comprehensive protection strategies that address both technological and human vulnerabilities.
Effective defense requires a multi-layered approach. AI-powered heuristic detection serves as the foundation, working alongside application whitelisting to restrict what programs can execute. Regular patching addresses known vulnerabilities before malicious actors can exploit them. Meanwhile, comprehensive backup strategies provide recovery options when prevention fails.
User education stands as perhaps the most critical defense component. The most sophisticated security technologies prove ineffective when users unknowingly execute malicious attachments or enable dangerous macros. Therefore, organizations must foster security-conscious cultures where employees recognize potential threats before infection occurs.
The battle against file infector viruses remains dynamic and challenging. As security technologies advance, so too do the methods employed by malicious actors. Nevertheless, combining technological safeguards with human vigilance creates resilient defense systems capable of withstanding even sophisticated attacks. Though complete security remains unattainable, understanding how these threats operate empowers users and organizations to substantially reduce their risk exposure in today’s complex digital environment.