What Are Unique Identifiers and Why Do They Matter?
In today’s digital ecosystem, every piece of data needs a distinct identity. Unique Identifiers (UIDs) serve as the digital fingerprints that enable systems to track, retrieve, and manage information with precision. Whether you’re building a database, managing user accounts, or tracking transactions, UIDs form the foundation of reliable data architecture.
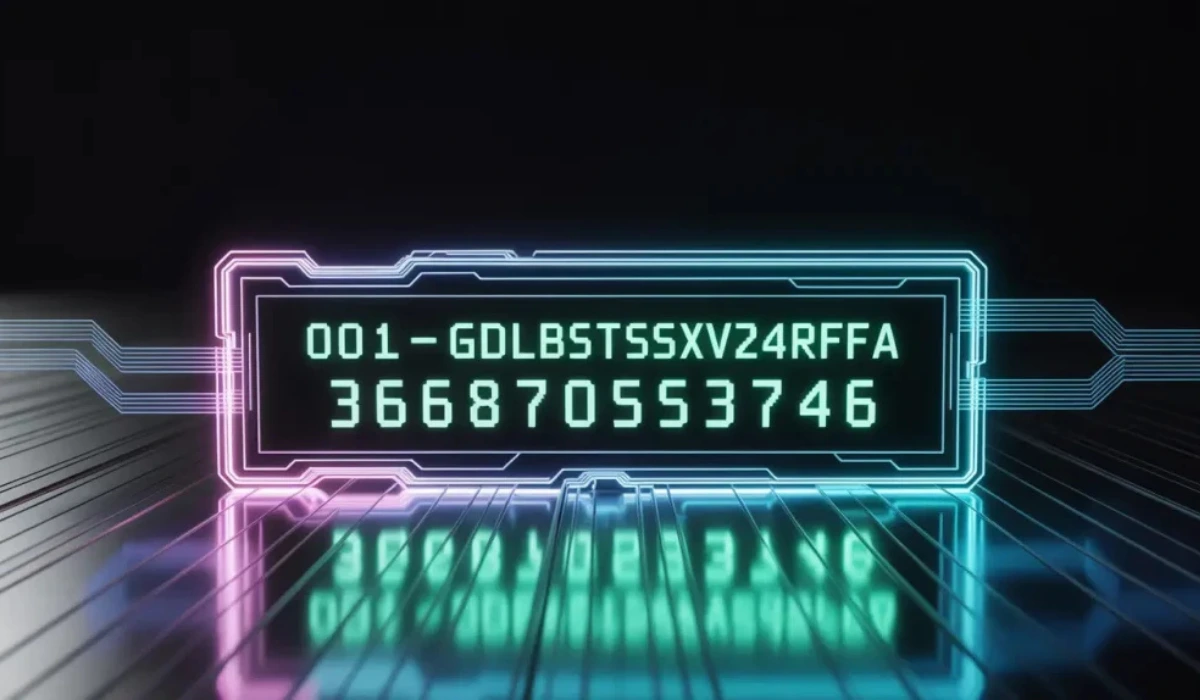
A unique identifier is a string of characters—often alphanumeric—that distinguishes one record from billions of others. Think of codes like 001-gdl1ghbstssxzv3os4rfaa-3687053746: complex, systematic, and designed for absolute uniqueness.
The Anatomy of a Well-Designed Unique Identifier
Core Components of UIDs
Modern UIDs typically contain several key elements:
Prefix Markers: The initial segment (like “001”) often indicates the data type, system origin, or version. This helps administrators quickly categorize and route information.
Encoded Information: The middle section frequently contains encoded metadata—timestamps, geographic indicators, or system-specific parameters. This embedded intelligence makes UIDs more than just random strings.
Hash or Random Components: Random alphanumeric sequences ensure collision-free identification across distributed systems. Advanced algorithms like UUID (Universally Unique Identifier) generate these with mathematical certainty of uniqueness.
Checksums or Version Numbers: Trailing digits may serve as validation checksums, ensuring data integrity during transmission and storage.
Why Modern Systems Rely on Unique Identifiers
Database Integrity and Relationships
UIDs serve as primary keys in relational databases, enabling seamless joins between tables. Without unique identifiers, maintaining data consistency across millions of records becomes virtually impossible.
Scalability in Distributed Systems
In cloud architecture and microservices, UIDs allow independent systems to generate identifiers without coordination. This distributed ID generation prevents bottlenecks and enables horizontal scaling.
Security and Privacy
UIDs obscure sensitive information. Instead of exposing sequential customer numbers or predictable patterns, complex identifiers protect against enumeration attacks and unauthorized data access.
Audit Trails and Compliance
Every transaction, modification, or access event can be traced through UIDs. This creates comprehensive audit logs essential for GDPR, HIPAA, and other regulatory frameworks.
Types of Unique Identifiers in Modern Applications
UUIDs (Universally Unique Identifiers)
The UUID standard generates 128-bit identifiers with negligible collision probability. Version 4 UUIDs are randomly generated, while Version 1 includes timestamps and MAC addresses.
Snowflake IDs
Developed by Twitter, Snowflake IDs combine timestamps, machine identifiers, and sequence numbers into 64-bit integers. They’re sortable, compact, and ideal for distributed systems.
Custom Format Identifiers
Many organizations design proprietary UID formats tailored to their specific needs, incorporating business logic, geographic codes, or hierarchical structures.
Cryptographic Hashes
SHA-256 or similar algorithms generate unique fingerprints for content verification, blockchain applications, and secure token generation.
Best Practices for Implementing Unique Identifiers
Choose the Right Length
Balance between uniqueness guarantee and storage efficiency. UUIDs offer 128 bits, but some systems optimize with shorter formats when appropriate.
Avoid Sequential Patterns
Sequential IDs are predictable and expose business metrics. Randomized or timestamped alternatives enhance security.
Consider Readability vs. Complexity
Human-readable formats improve debugging and customer support, but may sacrifice randomness. Strike a balance based on use case.
Plan for Future Scalability
Ensure your UID system can handle exponential growth. A format that works for thousands of records may fail at billions.
Implement Collision Detection
While rare, collisions can occur. Build retry mechanisms and validation checks into your generation logic.
Real-World Applications of UID Systems
E-Commerce Platforms
Order numbers, product SKUs, and transaction references all rely on UIDs. They enable tracking from warehouse to delivery, connecting disparate systems seamlessly.
Healthcare Information Systems
Patient records, prescription tracking, and medical device identification require failsafe unique identifiers to prevent life-threatening errors.
Financial Services
Bank transaction IDs, loan numbers, and account references use sophisticated UID systems to ensure accuracy in trillion-dollar operations.
IoT and Smart Devices
With billions of connected devices, unique device identifiers enable management, security updates, and data aggregation across global networks.
Technical Implementation: Generating Robust UIDs
Programming Language Support
Most modern languages offer built-in UID generation. Python’s uuid module, JavaScript’s crypto.randomUUID(), and Java’s UUID.randomUUID() provide standardized implementations.
Database-Level Generation
PostgreSQL’s gen_random_uuid(), MySQL’s UUID(), and MongoDB’s ObjectId generate identifiers at the database layer, ensuring consistency.
Distributed ID Generation Services
Dedicated services like Instagram’s ID generator or custom solutions handle high-throughput UID creation across multiple servers without conflicts.
Common Challenges and Solutions
Performance Bottlenecks
Centralized UID generation can become a bottleneck. Implement distributed generation with range allocation or hybrid approaches.
Storage Overhead
Long UIDs consume significant space in large databases. Consider compression techniques or shorter formats when appropriate.
Migration Complexity
Retrofitting UIDs into legacy systems requires careful planning. Implement gradual migration strategies with dual-key support during transition.
The Future of Unique Identification
Quantum-Resistant Identifiers
As quantum computing advances, cryptographic UIDs will evolve to maintain security guarantees.
AI-Optimized Formats
Machine learning systems may benefit from UIDs that embed feature vectors or classification metadata.
Cross-Platform Standards
Blockchain and decentralized systems are driving new standards for globally unique, verifiable identifiers.
Key Takeaways for Data Architects
Unique identifiers are more than technical necessities—they’re strategic assets that enable scalability, security, and system interoperability. When designing UID systems:
- Prioritize uniqueness with mathematical certainty
- Balance complexity with operational requirements
- Plan for distributed generation in cloud environments
- Implement robust validation and error handling
- Document your UID format and generation logic
The codes and identifiers powering modern applications represent careful engineering decisions that impact performance, security, and maintainability for years to come.
Frequently Asked Questions
What’s the difference between a UID and a GUID? UID (Unique Identifier) is a general term, while GUID (Globally Unique Identifier) is Microsoft’s implementation of the UUID standard. They’re functionally similar but may differ in format.
Can two systems generate the same UID? With proper implementation (like UUID v4), the probability is astronomically low—about 1 in 5.3 × 10^36. Practical collision risk is essentially zero.
Should UIDs be exposed in URLs? Sequential or predictable UIDs in URLs create security risks. Use opaque, random identifiers or implement additional access controls.
How do I migrate from sequential IDs to UIDs? Implement a dual-key system during transition, maintaining both old and new identifiers until full migration completes. Update application logic incrementally.
Are shorter UIDs always worse? Not necessarily. Context matters. For small-scale applications, shorter IDs may suffice. Evaluate your growth projections and collision tolerance.